- Power BI forums
- Updates
- News & Announcements
- Get Help with Power BI
- Desktop
- Service
- Report Server
- Power Query
- Mobile Apps
- Developer
- DAX Commands and Tips
- Custom Visuals Development Discussion
- Health and Life Sciences
- Power BI Spanish forums
- Translated Spanish Desktop
- Power Platform Integration - Better Together!
- Power Platform Integrations (Read-only)
- Power Platform and Dynamics 365 Integrations (Read-only)
- Training and Consulting
- Instructor Led Training
- Dashboard in a Day for Women, by Women
- Galleries
- Community Connections & How-To Videos
- COVID-19 Data Stories Gallery
- Themes Gallery
- Data Stories Gallery
- R Script Showcase
- Webinars and Video Gallery
- Quick Measures Gallery
- 2021 MSBizAppsSummit Gallery
- 2020 MSBizAppsSummit Gallery
- 2019 MSBizAppsSummit Gallery
- Events
- Ideas
- Custom Visuals Ideas
- Issues
- Issues
- Events
- Upcoming Events
- Community Blog
- Power BI Community Blog
- Custom Visuals Community Blog
- Community Support
- Community Accounts & Registration
- Using the Community
- Community Feedback
Register now to learn Fabric in free live sessions led by the best Microsoft experts. From Apr 16 to May 9, in English and Spanish.
- Power BI forums
- Forums
- Get Help with Power BI
- Service
- Re: Need help identifying who performed a XMLA Rea...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Need help identifying who performed a XMLA Read Operation that overloaded my CPU for 5 hours
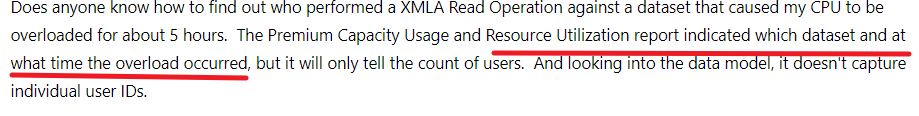
Does anyone know how to find out who performed a XMLA Read Operation against a dataset that caused my CPU to be overloaded for about 5 hours. The Premium Capacity Usage and Resource Utilization report indicated which dataset and at what time the overload occurred, but it will only tell the count of users. And looking into the data model, it doesn't capture individual user IDs.
And it appears that the Power BI audit logs don't capture XMLA Read Operations as an Operation to be tracked.
Any guidance on where to look is greatly appreciated.
Thanks
Solved! Go to Solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
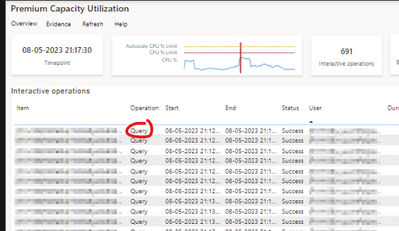
The Gen2 Metrics App will show you XMLA Read Operation, including the user running the queries.
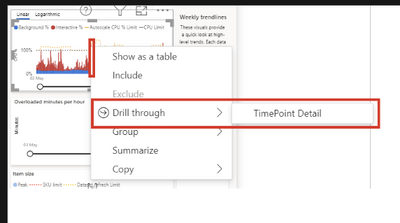
Use the drill trough TimePoint detail function to view operations at high CPU consumption period.
The screenshot above only shows "Query" but "XMLA Read Operation" will also be there if applicable.
Hope this helps!
Jeroen
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
The Gen2 Metrics App will show you XMLA Read Operation, including the user running the queries.
Use the drill trough TimePoint detail function to view operations at high CPU consumption period.
The screenshot above only shows "Query" but "XMLA Read Operation" will also be there if applicable.
Hope this helps!
Jeroen
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Could you find a solution yet? I am facing the same issue.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I haven't found a solution yet. Seems like a big miss on Microsoft's part.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @cperuski
after some research I was able to identify my users using the Power BI cmdltets to get the activity log
The activity log does not explicitly point out XMLA reads, but since there are only so many applications that cause XMLA reads it helped narrow down the search.
Because it was a reoccuring issue for me, I then also used the SQL Server Profiler during the hours when the overloading occured to get more specific information.
I hope this helps you
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I checked the internal icm, and there is indeed an issue that refreshes the CPU overload, which is still under investigation. ICM:295858845 If there is any news, I will update it here.
But for your question, there seems to be no way to find out who did it.
Best Regards,
Community Support Team _ Janey
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi, @cperuski
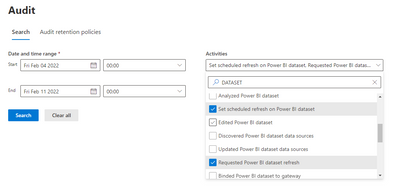
Although the XMLA operation can't be found in the audit log, but through the overloaded time, specific datasets, and certain operations of searching the dataset, the search target can be narrowed down in a large range, and then the related users can be found.
Audit log:
https://compliance.microsoft.com/auditlogsearch
Did I answer your question? Please mark my reply as solution. Thank you very much.
If not, please feel free to ask me.
Best Regards,
Community Support Team _ Janey
Helpful resources

Microsoft Fabric Learn Together
Covering the world! 9:00-10:30 AM Sydney, 4:00-5:30 PM CET (Paris/Berlin), 7:00-8:30 PM Mexico City

Power BI Monthly Update - April 2024
Check out the April 2024 Power BI update to learn about new features.