- Power BI forums
- Updates
- News & Announcements
- Get Help with Power BI
- Desktop
- Service
- Report Server
- Power Query
- Mobile Apps
- Developer
- DAX Commands and Tips
- Custom Visuals Development Discussion
- Health and Life Sciences
- Power BI Spanish forums
- Translated Spanish Desktop
- Power Platform Integration - Better Together!
- Power Platform Integrations (Read-only)
- Power Platform and Dynamics 365 Integrations (Read-only)
- Training and Consulting
- Instructor Led Training
- Dashboard in a Day for Women, by Women
- Galleries
- Community Connections & How-To Videos
- COVID-19 Data Stories Gallery
- Themes Gallery
- Data Stories Gallery
- R Script Showcase
- Webinars and Video Gallery
- Quick Measures Gallery
- 2021 MSBizAppsSummit Gallery
- 2020 MSBizAppsSummit Gallery
- 2019 MSBizAppsSummit Gallery
- Events
- Ideas
- Custom Visuals Ideas
- Issues
- Issues
- Events
- Upcoming Events
- Community Blog
- Power BI Community Blog
- Custom Visuals Community Blog
- Community Support
- Community Accounts & Registration
- Using the Community
- Community Feedback
Earn a 50% discount on the DP-600 certification exam by completing the Fabric 30 Days to Learn It challenge.
- Power BI forums
- Forums
- Get Help with Power BI
- Service
- Re: Need clarity around how to connect to Azure St...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Need clarity around how to connect to Azure Storage through a firewall
There are numerous posts on this forum about how to connect to Azure Storage when there is a firewall present. Here are some examples:
- https://community.powerbi.com/t5/Power-Query/Not-able-to-connect-with-storage-account-for-Azure-back...
- https://community.powerbi.com/t5/Service/Can-t-connect-storage-account-to-Power-Bi-Az-firewall-setti...
In all cases, a Microsoft representative recommends to "whitelist the IP address of the Power BI Service." This is not a reasonable answer. For one, the link being referenced is being deprecated in a couple of months (June 2020). Second of all, the referenced list of IPs is at the data center level, and accounts for thousands of IP blocks. An Azure Storage account can only support 100 IP rules in a firewall.
Either I am completely missing something, which is certainly possible, or this is a gap in Power BI Service. If I am not missing something: what is the correct way to use the Power BI Service with a secured Azure Storage account?
Solved! Go to Solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Once again, having to configure 300 rules is a non-starter because Azure Storage only accepts 100 IP ranges on a whitelist.
To close the loop on this, we have resorted to using an On Premise Data Gateway, which connects to Storage through the new Private Link service. It would be very helpful for the Power BI Service team to prioritize making Power BI Service a member of "Trusted Microsoft Azure services" so that this workaround is not necessary. Having to add an On Premise Data Gateway introduces a server into an otherwise serverless architecture. This server is one of the most expensive components of our solution and adds little value.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
2 years later... Has anything been done to be able to use Storage with PowerBI securely or we are still in Beta?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I don't believe you have to list each IP address individually, you an do ranges.
@ me in replies or I'll lose your thread!!!
Instead of a Kudo, please vote for this idea
Become an expert!: Enterprise DNA
External Tools: MSHGQM
YouTube Channel!: Microsoft Hates Greg
Latest book!: The Definitive Guide to Power Query (M)
DAX is easy, CALCULATE makes DAX hard...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes, this is correct. The IPs are presented as CIDR blocks in the referenced file and there are about 3000 of them in total and in some situations over 100 in a datacenter.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @phetzel1 ,
Try the reference below:
https://docs.microsoft.com/en-us/azure/storage/common/storage-network-security
Kelly
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have read through this documentation many times.
- VNET peering - Not applicable. Power BI Service not inside a VNET
- Private Endpoints - Not applicable. Power BI Service not inside a VNET
- Storage Firewall IP range exceptions - Not possible. There can be more than 100 IP ranges in a given datacenter (such as East 2)
- VNET/Subnet Firewall exceptions - Not applicable. Power BI Service not inside a VNET
- Allow Trusted Microsoft Services - To my knowledge, this does not cover Power BI Service
What is Microsoft's guidance when accessing a locked down Storage environment in Azure via Power BI? Is it an on-premise data gateway?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @phetzel1 ,
Best Regards,
Kelly
Did I answer your question? Mark my post as a solution!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
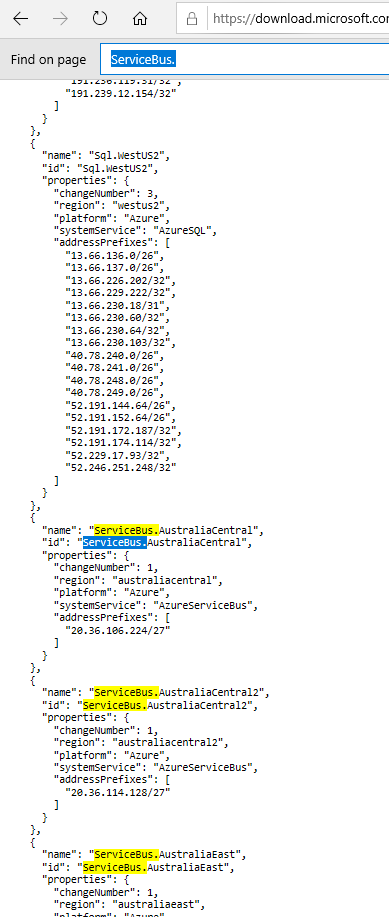
I feel like this is on the right track but unfortunately the list that you've referenced has greater than 100 IP address ranges for Service Bus. Azure Storage is only able to contain up to 100 IP address range exceptions. This is not a workable solution because we would have to leave out about 30 of the listed IP address ranges, not to mention we would not have any room to whitelist our analysts who want to connect to Azure Storage via Power BI Desktop.
What is the Microsoft recommended approach to view data in a secured Azure Storage account through the Power BI Service?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @phetzel1 ,
See details in the document of public I shared with you,find "ServiceBus.XXX",it is separated by region..About from the line 23000.
Kelly
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Based on your reply, I:
- Successfully created a dataset in Power BI Desktop based on data in ADLS Gen2
- Pushed that dataset to the Power BI Service, which is on the same tenant as the Azure Storage account
- Configured the Azure Storage firewall to include the IP address ranges for Service Bus in East US 2 and saved
When I attempted to create a refresh schedule for the dataset, based on both Oauth and Account Key authentication, I received this error message
I then temporarily turned the Storage firewall off and successfully gained access through Account Key authorization. This tells me that my authentication/authorization credentials are correct but I am still running into the same issue as before. I also added the IP Address ranges for Power Query Online in East US 2 without success. What is the Microsoft recommended approach to accessing a secured Storage account via Power BI Service?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @phetzel1 ,
Refer to the IP list used by service.Choose IP 33544-33873 in AzureCloud.eastus2,which you only need to configure about 300 rules.
But if available,you'd better use gateway,which you only need to configure some firewall rules in outbound port of the gateway machine,then configure the rules in ADLS2.
Here is the reference.
Kelly
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Once again, having to configure 300 rules is a non-starter because Azure Storage only accepts 100 IP ranges on a whitelist.
To close the loop on this, we have resorted to using an On Premise Data Gateway, which connects to Storage through the new Private Link service. It would be very helpful for the Power BI Service team to prioritize making Power BI Service a member of "Trusted Microsoft Azure services" so that this workaround is not necessary. Having to add an On Premise Data Gateway introduces a server into an otherwise serverless architecture. This server is one of the most expensive components of our solution and adds little value.