A new Data Days event is coming soon!
This time we’re going bigger than ever. Fabric, Power BI, SQL, AI and more. We're covering it all. You won't want to miss it.
Learn more- Power BI forums
- Get Help with Power BI
- Desktop
- Service
- Report Server
- Power Query
- Mobile Apps
- Developer
- DAX Commands and Tips
- Custom Visuals Development Discussion
- Health and Life Sciences
- Power BI Spanish forums
- Translated Spanish Desktop
- Training and Consulting
- Instructor Led Training
- Dashboard in a Day for Women, by Women
- Galleries
- Data Stories Gallery
- Themes Gallery
- Contests Gallery
- QuickViz Gallery
- Quick Measures Gallery
- Visual Calculations Gallery
- Notebook Gallery
- Translytical Task Flow Gallery
- TMDL Gallery
- R Script Showcase
- Webinars and Video Gallery
- Ideas
- Custom Visuals Ideas (read-only)
- Issues
- Issues
- Events
- Upcoming Events
Level up your Power BI skills this month - build one visual each week and tell better stories with data! Get started
- Power BI forums
- Forums
- Get Help with Power BI
- Developer
- Re: URL, Scope and Grant_type to use when creating...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
URL, Scope and Grant_type to use when creating a PBI REST API access_token?
Hello,
I have an app registered within Azure. I'm able to make a token request to login.microsoft.com and get a successful response and receive an access_token.
However, when I try to use this access_token to access the PBI REST API, I get a Forbidden Status 403.
If I use an access_token based on my own credentials, I can access the API.
What is the correct URL, Scope and Grant_type to use when creating a PBI REST API access_token for a Service Principal?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Awesome, thank you! I can't find ANY documentation on the allowed scope values to send to "https://login.microsoftonline.com/xxxxxxx/oauth2/token".
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
anyone, please help me with this, I've been stuck with the same error (403 forbidden). I have an app registered within Azure and even I can get the access token, but when I use the token to retrieve the datasets from API, it shows the above 403 error.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @Dayspring
Does your service principal have access to the workspace (through a security group or directly)?
Did you try to see the response body, sometimes it has additional info for the reason you get the error.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to provide access to the workspace and also please provide the list of scopes that I should use while authenticating, as of now, I'm using the below scopes.
openid
offline_access
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Dayspring each API has the list of required scopes, so it depends on which API you are using. You should follow the docs, for example: Reports - Get Reports In Group - REST API (Power BI Power BI REST APIs) | Microsoft Learn
For permissions you can either provide permissiong through Power BI portal as described here Roles in workspaces in Power BI - Power BI | Microsoft Learn or use an API to provide permissions Groups - Add Group User - REST API (Power BI Power BI REST APIs) | Microsoft Learn
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @ericOnline ,
Please refer to this thread:
Best Regards,
Liang
If this post helps, then please consider Accept it as the solution to help the other members find it more quickly.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for the response, however the Service Principal is listed as "Admin" in both the Workspace and Dataset. What I need is: Which token URL, Grant_type and Scope to use when requesting a token based on Client_id and Client_secret.
Please advise.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @ericOnline
Was your issue ever resolved?
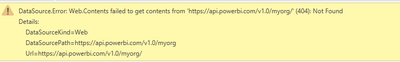
@V-lianl-msft I have very similar issue I have successfully brought back the token correctly now using a script provided by one of your team but I am now getting
The only thing I am missing in my script is "Scope" as I am unsure what to use?
This is the post for reference
https://community.powerbi.com/t5/Desktop/Refreshable-Token-for-Admin-Rest-API/m-p/3152512#M1065083
This is the script I used from the above post
let //get token url = "https://login.microsoftonline.com/xxxxxxx/oauth2/token", GetJson = Web.Contents( url, [ Headers = [ Accept = "application/json", ContentType = "application/x-www-form-urlencoded" ], Content = Text.ToBinary( "grant_type=client_credentials& client_id=xxxxxxx& client_secret=xxxxxxx& scope=xxxxxx" ) ] ), token = Json.Document(GetJson)[access_token], //other api usage wiht above token Result = Web.Contents( "https://xxxxx.xxx.com", [ Headers = [ #"Content-Type" = "application/json", Authorization = "Bearer " + token, RelativePath = "/xxxxx/xxxxx" ] ] ) in Result
Do I need to add anything else to the script apart from the scope?
Thanks
Karen
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I struggled for a few days with the forbidden (403) error and it turned out that I had the App registration correct. What I needed to do was to call the scope correctly in get_token. I was passing ".default" and then I read a thread where it recommended to change it to
Helpful resources

Power BI Monthly Update - April 2026
Check out the April 2026 Power BI update to learn about new features.

Data Days 2026 coming soon!
Sign up to receive a private message when registration opens and key events begin.

New to Fabric Survey
If you have recently started exploring Fabric, we'd love to hear how it's going. Your feedback can help with product improvements.

| User | Count |
|---|---|
| 4 | |
| 2 | |
| 1 | |
| 1 | |
| 1 |